Fake Apps, Infiltration & Exchanges Held Hostage: The New Crypto Threat Matrix
You felt it, didn’t you?
That little jolt of unease when you heard the news.
A fake Ledger app… one of the most trusted names in self-custody… somehow slithered its way onto the Apple App Store.
This wasn’t some dark web scam… it was a Trojan horse delivered right to the gates of the digital fortress.
The unfortunate thing is that this isn’t an isolated incident… frankly, it’s just the opening salvo in a new, terrifying phase of the war on your financial sovereignty.
The attacks are becoming more sophisticated… more systemic… and they’re coming from every direction… from lone wolves to entire nations.
Scams Where You Least Expect Them
The first strike was personal… a fake version of Ledger Live… “the official wallet app”… appeared on Apple’s highly curated App Store.
Seems impossible right?
For a brief window… anyone searching the Apple app store for a way to secure their Bitcoin and crypto could have downloaded a perfect-looking counterfeit… designed to steal their seed phrase.
Think about that…
It’s like finding a fake ATM in the lobby of your own bank… it’s a brutal violation of trust, proving that even the “walled gardens” we rely on for security have cracks in their walls.
Obviously this “Ledger app” was anything but official… even though it was not flagged by Apple.
Why wasn’t it flagged though?
Understanding Is Your First Layer of Defense
The answer to that question is probably already obvious to those who have a more intimate knowledge of crypto and wallets…
Ultimately, the reason for it all is because this fake app… it didn’t actually contain any malicious code that would ordinarily be detected…
This whole scheme… it was a bait & switch… directing those who download it to a fake site… once there it asked them to enter their seed phrase…
In hindsight… the “red flags” were there… at least for those who are familiar with the workings of crypto, and hardware wallets.
Are you familiar with how crypto works?
Do you understand hardware wallets?
Let me be brutally honest… even if you think you do… you can always use more education… afterall, your literal life savings depend on it!
Here are a couple of resources to help…
Let’s begin with a seed phrase.
Do you know what it is… what it does?
You should… start here to do just that… but if you want a full grasp of the power of your seed phrase… don’t skip this.
Then, once you have an understanding of seed phrases… may I suggest, you learn how to properly secure it.
And… if you’re looking for an easy to use hardware wallet… may I suggest Tangem.
The bottom line is that the message is clear… you cannot trust a logo… or a download button in an app store to protect your assets.
The ultimate responsibility for security falls on you, and you alone.
The Real World Consequences
Unfortunately even when you try to do everything right… DCA into Bitcoin for years… secure your Bitcoin in a hardware wallet… one mistake can erase all that work…
That’s exactly what happened here…
Musician Garrett Dutton, known by his stage name G. Love, lost his entire retirement savings… nearly 6 Bitcoin worth over $424,000… to this exact scam.
While setting up a new Apple computer, he searched the Mac App Store for Ledger Live, downloaded the fake app, and entered his 24-word seed phrase when prompted.
The moment he entered his master key, the attackers drained his wallet.
As he put it,
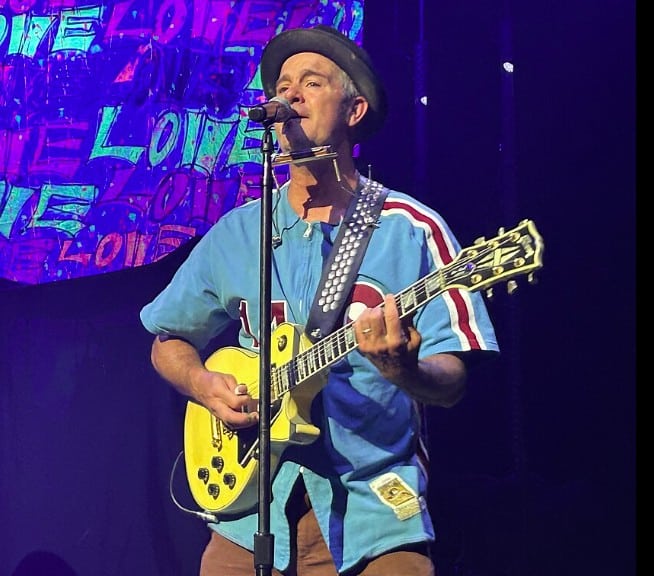
“I lost 5.9 BTC all I had for ten years I worked on this f#ck be careful out there.”
This is the brutal reality of the new threat landscape… a single moment of misplaced trust… even on a supposedly secure platform… can wipe out a lifetime of work in an instant.
Right now you might be thinking… “there’s got to be some way to get his BTC back.”
This is highly unlikely… learn why here.
Unfortunately, for thefts like this… the issue is often user error…
Targeting Central Points of Failure
But the assault doesn’t stop at the level of individual apps… the enemy goes after the infrastructure itself.
Case and point… Kraken, one of the largest and most established crypto exchanges, revealed it is being actively extorted by criminals threatening to release sensitive user data.
This isn’t just about stealing funds anymore… it’s about holding the entire exchange hostage.
This type of attack goes far beyond the cryptocurrency itself… it’s about data… about the personal information of customers… it’s about control…
Knowing this, the question becomes… why would you let someone else hold the keys to your kingdom… especially when they can be held at gunpoint?
This attack exposes the fundamental weakness of centralized custody… it’s a honey pot… a treasure trove for hackers to target… it’s a single point of failure.
Kraken has said it has located the employee who has assisted hackers… and this employee has since been fired… the damage is done.
As of the writing, Kraken says it will not give in to hackers demands for ransome.
But this is a powerful, real-world demonstration of why self-custody isn’t just a philosophical preference… it’s a tactical necessity.
Attacks Getting More Coordinated
Please realize that these aren’t random, disconnected events… they’re fronts in a coordinated and rapidly escalating assault…
On one side, you have sophisticated cybercrime syndicates like the ones extorting Kraken… on the other, you have nation-states…
The recent investigation by on-chain sleuth ZachXBT uncovered a sprawling network of North Korean IT workers infiltrating crypto companies… not as hackers from the outside… but as trusted employees on the inside.
This is a whole level of threat.
Combine this with news of data breaches at physical ATM operators like Bitcoin Depot, and the picture becomes undeniable.
The system is being probed and attacked from every angle… software… hardware… and even human resources.
They aren’t just trying to pick the lock anymore… they’re trying to steal the whole building!
In this episode of Matrix Money, CryptoJar and I discuss all of it
Make Education Your First Defense
One thing is for certain… the game has changed.
The threats are no longer just about phishing emails or weak passwords. They are systemic… targeting the apps you use… the exchanges you trade on… and the very people who build the technology.
The walls of the old system are not just crumbling… they are being actively… and intelligently breached.
If you’re looking for tools to protect yourself in this space… visit the My Toolbox page… everything I use, and recommend is there…
In this new environment, self-custody and personal security are no longer optional… they are the only viable path to true financial freedom.
The choice is no longer about fixing their system.. it’s about building your own fortress from the inside… step-by-step.
Disclaimer
The information provided here is for INFORMATIONAL & EDUCATIONAL PURPOSES ONLY!
View our complete disclaimer on our Disclaimer Page