Can Someone Steal My Cryptocurrency With My Wallet Address?
Last updated on June 8th, 2023 at 03:20 pm
You make cryptocurrency investments because you are looking to increase your wealth and create a stable financial future for yourself and your family.
In crypto, you are the bank. So, once you’ve made your investments it is up to you to keep them safe. A cryptocurrency wallet will help you to do this, but you might be wondering if someone can steal your crypto if they have your wallet address..
The wallet address or public key can not be used to steal money from a cryptocurrency wallet. It is a send only address which allows for the transfer of crypto assets to the wallet. Cryptocurrency can be stolen from a wallet with the private key. The private key must be kept protected for maximum wallet security.
Just because a wallet address doesn’t provide access to the crypto in your wallet, that doesn’t mean that there is no threat to your cryptocurrency. Hackers utilize many different attack vectors in order to steal your cryptocurrency.
You need to know the different ways a hacker will try to get your crypto and what you can do to protect your investments. Let’s discuss how you can do just that.
How Can Crypto Be Stolen From My Wallet?
While no cryptocurrency wallet can be considered 100% safe, some wallets are safer than others. The safer wallets provide less opportunities for hackers to have access to them.
Cryptocurrency can be stolen from a wallet if the hacker has access to the private key. Crypto can also be stolen if the hacker is able to gain access to the cryptocurrency exchange, or exploit a vulnerability in the wallet software, or exploit a vulnerability in the device the wallet is operating on.
Most people new to the crypto space are often introduced to cryptocurrency wallets that are much less secure. This is because these wallets generally have a much easier to use interface or are on the cryptocurrency exchanges people are using.

Higher Risk Wallets
This category of crypto wallet is called a hot wallet. There are several different types of wallets in this category. They vary in the way you access them as well as who controls them.
Hot wallets provide hackers the greatest opportunity to steal your crypto.
Wallets that fall into this category include cryptocurrency exchange wallets, online (web) wallets, mobile wallets and desktop wallets. Each of these wallet types provide hackers with multiple points of attack.
The highest risk wallet in this category is a cryptocurrency exchange wallet.
This is because an exchange provides the hacker with a large honeypot that makes it worth their time and effort to hack.
But when you’re dealing with a centralized cryptocurrency exchange, the list of potential risks to your cryptocurrency increase exponentially.
Some previous cryptocurrency exchange hacks and losses include the Bitfinex hack, CoinExchange closing its doors, Einstein exchange goes belly up, IDAX CEO disappears with everyone’s crypto and Bitpoint exchange suspends services.
To add insult to injury, crypto exchange wallets have the added disadvantage of being a custodial wallet.
This means that the cryptocurrency exchange controls your crypto (private key), so technically, they own your crypto.
This idea of a custodial wallet also goes one step further when it comes to centralized exchanges. Keep in mind that these exchanges are going to comply with whatever their jurisdictional government requires.
So for example, they will turn over user information or freeze funds whenever a government agency asks.
This is exactly what happened in Canada when the truckers tried to use cryptocurrency after the government froze their bank accounts while they were protesting against Covid restrictions.
But that’s not the first time this type of thing has happened, some other examples include Switzerland freezing Russian crypto and Starling Bank suspending deposits.
PRO TIP: Never leave your cryptocurrency on an exchange unless you are actively trading these assets.
The next highest risk wallets in this category are online or web wallets.
This is primarily because these wallets are always online and available for hackers. Not to mention that the internet connection you use also provides hackers with an additional point of access.
SECURITY TIP: Always use a VPN (Virtual Private Network) while accessing anything online.
The next most vulnerable type of wallets in this category are desktop and mobile wallets.
These wallet types are vulnerable to hackers mostly because of the devices they are used on. So, having malware or a virus for example, on your phone or computer, provides hackers access to all the information on there, including your cryptocurrency.
Some of the hacks and thefts with online wallets include Chrome extensions stealing crypto, hacker groups targeting Mac OS and malware affecting Windows devices.
PRO TIP: Use a separate phone or computer ONLY dedicated to accessing your cryptocurrency wallet.
Lower Risk Wallets
Cold wallets provide hackers a minimum opportunity to steal your cryptocurrency.
This category of wallets include paper wallets and hardware wallets.
Due to their limitations and difficulty of use, paper wallets are mostly obsolete. Today, they are primarily used in conjunction with Bitcoin ATMs.
In this category, a hardware wallet provides a high level of security while still giving you control of crypto (private keys).
These wallets conduct transactions with your private keys in an offline environment. Because of this, these wallets have little or no interaction with an online connection, so that eliminates most of the possible ways a hacker could gain access.
SECURITY TIP: Only purchase a hardware wallet directly from the vendor. There is no guarantee that wallets purchased from a third party vendor have not been tampered with.
I use and recommend Ledger and Trezor hardware wallets.
Understanding all you can about wallets is important. I’ve detailed the different types of cryptocurrency wallets to help you decide what ones are best for you, check that out here.
In order to best protect yourself and your crypto assets, it’s good to know how these hacks can occur.

Methods Used To Hack Crypto Wallets
Cryptocurrency wallet developers strive to create the most secure wallets possible.
Afterall, what developer wants their product associated with a major crypto theft?
However, hackers still look to exploit whatever opening they can to get not only your personal information, but your cryptocurrency as well.
Fake or Infected Wallets
One of the most effective ways of capturing your cryptocurrency is by intercepting it as you are trying to secure it.
This can happen in a few ways, but the most common way is for a hacker to purchase a hardware device, infect it with malware and sell it on a third party platform such as eBay or Amazon.
Then an unsuspecting crypto investor buys this wallet and adds their cryptocurrency to it, thinking it’s safe. Unfortunately, at some point in the future they find out that their crypto is gone.
What happened?
When they set up the wallet and transferred their cryptocurrency private keys to it, the malware took over and sent the private keys to the hacker. The hacker then uses these keys to access the cryptocurrency on the blockchain and steals it.
In a slightly different version of this, a more sophisticated hacker will pose as the hardware device manufacturer. They will send a ‘new’ hardware device to someone who already has one. They will include a letter saying that their current device is vulnerable and they need to move their cryptocurrency on this replacement device.
Once the unsuspecting crypto holder does this, the malware installed on this device notifies the hackers.
The end result, your crypto gets stolen.
SECURITY TIP: A hardware device manufacturer will NEVER send you a replacement device without you requesting one.
But hardware wallets are not the only ones that are susceptible to attack.
Phishing Attacks
Phishing attacks have been a tool in the hackers toolbox for a long time.
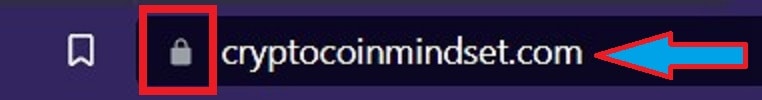
In a phishing attack, a hacker creates a fake website which looks identical to the real website.
The only difference is the URL.
So for example, if a hacker was trying to get the login credentials for someone who uses Coinbase, they would create a fake site with a URL like Coinbase.co instead of Coinbase.com.
Once the unsuspecting user logs in on the fake website, the hacker now has the necessary information to login on the real website and drain all the users crypto from the platform.
This type of attack can also take the form of an email.
The hacker emails a crypto exchange user and says for security reasons they need to update their login info… and of course, the hacker provides a convenient link in the email.
Unfortunately that link leads the user to the hackers fake site, and the end result is the same as before.
SECURITY TIP: Check a website URL to ensure it’s spelled correctly, has the correct TDL (ie; .com or .net) and there is an SSL indicator. See example below
While phishing attacks are a treasure trove for hackers to compromise crypto wallets, infecting a user’s phone or computer can sometimes be even more effective.
Malware and Viruses
Keeping your cell phone and computer free of viruses and malware will help prevent the loss of your identity, your money and your cryptocurrency.
This is also something that has been in the hacker toolbox for a long time. The only changes to this attack are the types of malware and viruses, what they do, and how they are delivered.
Believe it or not, people still click on suspicious links. Once a link is clicked any number of things can happen.
You can be a victim of a phishing attack as we mentioned a moment ago, or you can be directed to a website that is infected with a worm that makes its way onto your device and begins searching for sensitive information to send back to hackers.
Either way, your cryptocurrency is only as safe as the device your wallet is on.
Using 2FA (two factor authentication), such as Google Authenticator or Authy is a good practice… at least until your cell phone gets compromised.
2FA Exploits
Many people already use 2 Factor Authentication (2FA). Two of the most popular authenticators are Google Authenticator and Authy.
They provide an additional layer of security by creating randomly generated numbers on your cell phone. Each generated number corresponds to a specific platform or website that requires you verify yourself when logging in.
This is similar to the functioning of public and private keys in crypto.
Remember, the apps on your phone are only as secure as your phone.
The most common way for hackers to gain access to your 2FA is via a SIM swap.
This is done when a hacker contacts a cell phone provider and impersonates the user and gets the company to swap SIM card control from the owner to the hacker.
These kinds of attacks are very common, mostly because our personal identifying information (PII) has been lost by the people we rely on to keep it safe.
Once this information is available on the dark web, it can be used for all sorts of nefarious acts.

Social Engineering Attacks
One thing is for certain when it comes to cryptocurrency security… We are by far the weakest link in the security chain!
Most of us don’t think about it like that though, we think to ourselves, I would never give someone access to my crypto.
And while that may be your intention, hackers are resourceful.
Social engineering attacks take on many forms, some of which we’ve already discussed, like phishing and malware.
In essence, they are attacks that rely on personal interaction. Through those interactions a hacker tries to get you to break with your normal security procedures.
Using these social interactions they can gain access to your cryptocurrency exchange, a cryptocurrency platform or even your cryptocurrency wallet. All looking like they are helping you close a potential security vulnerability.
And we believe them… because we all want to protect our crypto.
These interactions can come in any form, email, text or call.
Remember these cryptocurrency exchanges are not going to reach out to you for your information, they already have it.
These crypto platforms are not going to need your login info, they already have it.
Cryptocurrency wallet providers and manufacturers are not going to reach out to you about a security issue nor are they going to send you a replacement wallet without your requesting one.
The best way to not fall victim to these types of social attacks is to establish solid security procedures and protocols and not vary from them.
However, sometimes your wallet can fall into the wrong hands… and that doesn’t necessarily just mean a hacker.
Hardware Attacks
Should a hardware wallet fall into the hands of a malicious actor, such as a hacker, the wallet becomes susceptible to an entirely new set of attacks.
Remember, hardware wallets conduct their transactions in an offline environment. However, if a hacker has a physical device, they can attempt to crack the device in other ways.
Some of these attack vectors include power glitching and side channel attacks.
If you lose your hardware wallet, you should import your wallet to another device and then move it to a new hardware wallet with a different seed phrase.
However, if the hacker was able to get physical control of your hardware wallet, you may have also been attacked physically by the hacker.
Personal Attacks
Unfortunately, sometimes we can make ourselves a target for crypto thieves.
Again, once our personal information is out there for hackers to find, it becomes easy for us to be the ultimate target. So, it’s a good idea to think with a security mindset.
One of the most important things you can do is to not tell anyone about all of your cryptocurrency holdings.
As crazy as this sounds, this includes family. People like to talk and brag and this can invite trouble.
However, this doesn’t mean you can’t talk about crypto… by all means, please tell everyone… the more people involved the better!
But, be smart about what you tell people.
Help to educate people, point them in the right direction, show them how to create a passive income with crypto and how to invest in crypto for their family’s future.
Educating yourself about crypto is important, let my ebook help. Get it here.

Protecting Your Crypto
So as you can see, there are a lot of opportunities for a hacker to steal your cryptocurrency. The good news is, by following a few steps you can keep your crypto safe.
The best way to prevent cryptocurrency theft is by using a hardware wallet and securing your private keys, using strong passwords, keeping your device operating systems updated, using firewalls and virus protection, using a secure internet connection, using a VPN and security keys.
While this may seem like an exhaustive list, once set up, it can be easily incorporated into your standard security protocols.
Secure Your Passwords and Private Keys
Private keys are your cryptocurrency. They represent your crypto on the blockchain. Keeping them backed up and secure is paramount.
Consider having your private keys written down or saved on air-gapped devices in multiple locations. If possible, in different geographic locations, to protect against catastrophic events like a tornado or flooding.
The same is true for your passwords. You may want to consider a password manager to help you. I use and recommend NordPass.
However, even if you use a password manager, I suggest still having a written or saved backup on an air-gapped device.
When creating your password, make sure it is strong, so it can not easily be guessed. You can use a random password generator, but if you choose to do it yourself, consider these tips:
Your passwords should be a minimum of 8 characters.
These characters should contain upper and lower case letters, numbers and symbols. Don’t use any personal information or words out of the dictionary.
Having good password management is critical when dealing with anything online, so much so, that I took the time to write an entire article about it, you can read it here.
Keep Operating Systems Updated
One of the easiest ways for a hacker to get ahold of your cryptocurrency is to exploit the device your wallet is stored on.
Even if you use a hardware wallet, the manufacturers will occasionally send update notifications to users. You should always update your hardware device when necessary.
SECURITY TIP: Only update your hardware device directly from the manufacturers website.
Some of your crypto wallets may be located on your cell phone or computer. Most cell and computer providers will create automatic updates for your devices.
However, this is an increasing attack vector for hackers, so you should periodically check to ensure you are running the latest version of your device operating system.
Use Firewalls and Antivirus
It is always a good idea to protect your devices with antivirus software and firewalls. These days, most antivirus software bundles in firewall protection, so it’s easy to get double the protection.
But like most things, in order for these software programs to be effective they must be continually updated. There are new threats discovered online everyday, so be sure you are running the latest version of software.
Use a Secure Internet Connection
Using an open wifi connection is rarely a good idea. This connection is not secure, even if you have to sign a user agreement to access it.
This is not because the connection itself has a virus to infect your device, but rather because there could be other users on the wifi waiting to attack you.
You should always use an encrypted wifi connection whenever possible. If such a connection is not available, consider using your mobile data as this is most often encrypted.
Use a VPN
In today’s day and age, it is reckless to not use a VPN (Virtual Private Network).
A VPN helps you to encrypt the connections you make online. It is like a tunnel that only allows you to drive in it.
I use Torguard on all of mine and my family’s devices. It doesn’t not slow my internet or data connections and frankly, it’s the best I’ve used.
Use code CCM at checkout and save 50%.
As a matter of fact, I believe that using a VPN is so important that I’ve dedicated an entire article to the subject. Head over here to read it.
Use a Security Key

Two factor authentication is something that should be a given these days.
However, as we mentioned earlier when discussing 2FA exploits, sometimes these apps on your phone are susceptible to SIM swaps.
Whenever possible I use a multi-factor device called Yubikey.
Much like it sounds, this is a device that looks a bit like a small key, but it’s scanned by or plugged into your device to authenticate who you are.
Yubikey is compatible with many cryptocurrency exchanges as well as other websites you probably use every single day.
I recommend adding YubiKey as an additional layer of security for everything you do online.
I have created a very in-depth article covering the importance of crypto related security. Taking time to review this critical information can be the key to keeping your cryptocurrency investments safe.
Bringing It Together
Let’s pull together what we’ve covered.
To start, nobody can steal your cryptocurrency with just your wallet address. This is a send only address.
In order to steal the cryptocurrency in your wallet someone would need your private keys. So, protect and backup your private keys.
Not all wallets are created equal. Hot wallets are at higher risk of being hacked than cold wallets.
These attacks can come from many different vectors including fake or infected wallets, phishing attacks, malware and viruses, 2FA exploits, social engineering attacks, hardware attacks and personal attacks.
However there are steps you can take to help increase your security. These include securing your private keys, using strong passwords, keeping your OS up to date, using firewalls and antivirus as well as using a secure internet connection, VPN and security key.
Items Related To Your Wallet Address
What is the safest Bitcoin wallet?
Bitcoin should be a big part of your cryptocurrency portfolio. Having a safe, secure place to store it is important. We Discussed The Safest Bitcoin Wallet Here.
Why is security important in crypto?
Though online security is important no matter what you are doing on the web, it reaches an entirely new level when you are dealing with cryptocurrency. Read Why Security Is Important In Crypto Here.
Disclaimer
The information provided here is for INFORMATIONAL & EDUCATIONAL PURPOSES ONLY!
View our complete disclaimer on our Disclaimer Page